In reel life, you can see Jason Bourne, James Bond, many a hero and villain in spy and crime thrillers manipulating identity papers, breaking into electronically secured doors, hacking systems and crossing borders with false identity documents. Forging documents is an old trade. It has been a source of worry for security establishments, bankers, financiers, business people and individuals.
One of my earliest brushes with electronic security systems go back to early years of the last decade. We, in Tata Consultancy Services, were pursuing the ambitious UK E borders advanced passenger information project. Since then, security technology has evolved and greatly improved.
Technology now enables us to detect document fraud in just a few seconds. Scanning systems supported by powerful algorithms are able to detect manipulations to images. High speed data transmission has made it possible for us to send and receive documents all across the globe.
Data is now routinely sent across networks in an encrypted format. This makes it difficult for hackers to hack, decode, steal and misuse the data in transit. Applications are no longer needed to be installed on each and every device. These can be downloaded from the cloud. Updating and maintenance of such cloud-based systems can be done conveniently.
Document handling costs have dropped with the induction of this technology. Processing has become faster. If the system runs autonomously, cost savings as a result of reduced manpower would increase. Such systems will eliminate the risk of human errors and omissions. Faster processing will also mean an enhanced ability to handle larger volumes of data, higher process efficiency, and better margins.
Financial fraud is a major challenge faced today by bank and financial services providers. The financial services industry has tried to protect itself by bringing in checks at multiple levels. Checking customer identity is one such check. Customers need to bring identity documents in original, and get these verified in person before being permitted to open an account, receive a loan, and avail of other critical services.
Loans, investments, opening bank accounts, even obtaining a new telephone connection, a driving license and a many other transactions and access to variety of services require a KYC (Know Your Customer) document check. In many countries KYC verification is mandatory.
Identity verification has become all the more critical in the light of threat from terrorists, infiltrators and impersonators. Transacting companies, security organizations have been obliged to take on more staff to conduct physical document checks.
The volumes of people and transactions requiring identity document checks are particularly high at border control points and banks. An automated system that can do away with the human interface will lead to not just reduced manpower costs but faster turnaround, reduced waiting time, and enhanced customer satisfaction.
Banks and financial services are taking place increasingly online. Customers prefer the convenience of their homes and offices to conduct business. If the KYC process can be conducted remotely that will be a huge customer convenience.
In order to understand the developments in security technology, I got down to having a chat with Ofer Friedman Vice President of Au10tix Limited; a Cypress-registered company. Au10tix is a subsidiary of ICTS International. ICTS International is a NASDAQ-listed security firm founded by intelligence, military, and security experts.
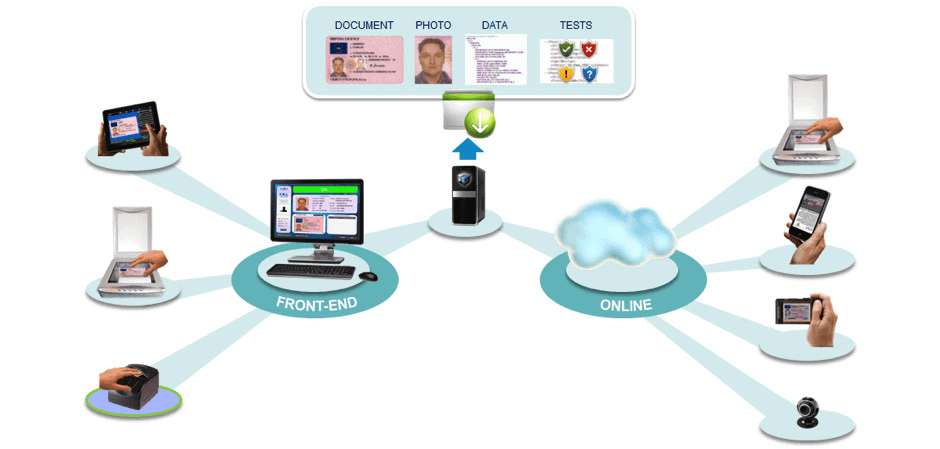
Au10tix’s team of electronic security experts is based out of Israel. It is this team that has developed document verification technology proprietary to the company. With the help of the system, identity documents are scanned and verified. Documents can be submitted to the system both in physical and electronic format. Physical documents are scanned, authenticated, and verified in just ten seconds, the company claims, on a system that is fully autonomous.
Documents sent from remote locations digitally can be checked and processed by the system. Authentication is done over the cloud. The system can verify and map documents against hot lists, anti terrorist and other databases. This makes the process robust and comprehensive.
I was told by Friedman that the solution can detect inconsistencies in a document like detecting a forged picture and manipulation of the text. Most other systems, he said, have the capability to detect image fraud only. Au10tix system can identify manipulations to a text too.
The application can work standalone. It can also be integrated into an existing solution. For example, in case it is deployed in a bank the system can be integrated with an existing banking solution. Integrated, the entire system is able to operate seamlessly. Friedman states that this is an integrated API portal-based solution. However, I do believe that full integration will require the writing of some bit of code for it to perform seamlessly with an integrated banking solution.
Document processing and authentication, as mentioned earlier, are done in a virtual private cloud environment providing an extra layer of security. When asked if the solution could be deployed on a standalone server located within an organization, Friedman replied in the affirmative. Such capability becomes relevant for clients with intelligence, national security, and the military.
A geopolitical or security threat is never far away for such clients and installing the system in a server on location becomes a critical requirement. The system, according to the Au10tix website can be integrated with biometric readers, barcode readers, magnetic strip and chip readers, signature pads, etc.
Friedman claims that the Auto10tix solution is unique and comparative solutions are not available in the market. The algorithm, the company website claims has machine learning capability. The application is said to be available in multiple languages.
Going forward Au10tix technology probably with modifications can be used to verify larger businesses and other documents too. These too are subject to manipulation for pecuniary and other purposes. We probably will see more updates and refinements in the future. This, though, even in its current state is a very useful solution appropriate to the need as it exists today in 2016.